How to create a vpn profile in microsoft intune step by step guide 2026
How to Create a VPN Profile in Microsoft Intune Step-by-Step Guide 2026: Quick Start to Secure Access and Modern Management
How to create a vpn profile in microsoft intune step by step guide 2026? Here’s the plain answer: you’ll create a VPN profile in Microsoft Intune by configuring the VPN connection settings in the Intune portal, assign the profile to the right devices or users, and deploy it through a policy. This guide breaks down everything you need to know, with real-world steps, tips, and best practices to get you up and running fast.
Quick fact: In 2026, more than 80% of mid-to-large organizations rely on Intune for VPN profile management as part of their zero-trust and mobile device management MDM strategy.
If you’re wondering how to create a VPN profile in Microsoft Intune step by step guide 2026, you’re in the right place. This guide is designed to be practical, not just theoretical. We’ll walk you through the planning, setup, testing, and troubleshooting stages with a mix of steps, checklists, and real-world tips. Expect bite-sized sections you can skim or dive into, plus visuals you can replicate. Troubleshooting Sophos VPN Why It Won’t Connect and How to Fix It: Quick Tips, Power Settings, and Real-World Fixes
What you’ll learn
- How to prepare for an Intune VPN profile deployment
- The exact steps to create a VPN profile Windows and iOS/macOS focused
- How to configure connection settings for common VPN protocols IKEv2, SAML, certificate-based, and always-on VPN
- How to assign VPN profiles to devices and groups
- How to verify and test VPN connectivity
- Common issues and quick fixes
- Helpful resources and best practices for ongoing management
Useful resources and URLs text only Apple Website - apple.com Microsoft Learn - docs.microsoft.com Intune Documentation - learn.microsoft.com Windows IT Pro Blog - blogs.windows.com Reddit Tech/MDM Subreddits - reddit.com/r/MDM VPN Protocols Overview - en.wikipedia.org/wiki/Virtual_private_network OpenVPN - openvpn.net NordVPN - nordvpn.com Cisco AnyConnect - cisco.com IKEv2 VPN - en.wikipedia.org/wiki/Internet_Key_Exchange Certificate Authority overview - en.wikipedia.org/wiki/Public_key_infrastructure
Section 1: Why use Intune VPN profiles in 2026
- Centralized management: One console to push VPN settings to Windows, iOS, and macOS devices.
- Policy-driven access: Combine with conditional access to enforce compliance before a VPN connection is allowed.
- Modern security posture: Support for certificate-based auth, SAML/SSO, and always-on VPN for seamless user experience.
- Efficient onboarding: Automate profile creation during device enrollment or app provisioning.
Stat snapshot
- Surveys show organizations deploying VPN profiles via Intune see 20–40% faster device onboarding and a 15–25% reduction in help desk tickets related to VPN configuration.
- For Microsoft 365 tenants, conditional access policies tied to VPN sessions reduce risky sign-ins by a noticeable margin.
Section 2: Planning before you create the profile Ubiquiti VPN Not Working Here’s How To Fix It Your Guide: Quick Fixes, In-Depth Tips, And Pro Tips
- Define the VPN protocol: IKEv2 is common for enterprise, but SSTP or SSL VPN may be needed for legacy endpoints.
- Choose authentication method: certificate-based, username/password with RADIUS, or SAML-based with Azure AD.
- Decide on device groups: Create security groups for Windows devices and for iOS/macOS devices to target the right users.
- Prepare certificates: If using certificate-based auth, ensure your PKI is ready certificate templates, trusted root CA, and distribution via Intune or a CA server.
- Consider always-on VPN: If your use case requires persistent tunnels, plan for Windows 10/11 Always On VPN configurations and split-tunneling policies.
Section 3: Create a VPN profile for Windows devices IKEv2 with certificate-based or user auth Step-by-step:
- Sign in to the Microsoft Endpoint Manager admin center portal.azure.com and go to Devices > Configuration profiles.
- Create profile -> Platform: Windows 10 and later; Profile type: VPN.
- Basic info: Provide a clear name like “VPN - IKEv2 Always On – Windows 11” and add a description for future admins.
- Connection name: Enter a VPN connection name that matches your VPN server e.g., “CorpVPN”.
- Server address: Put the VPN server address FQDN or IP.
- Connection type: Choose IKEv2 or IKEv2 with certificate.
- Authentication method: If certificate-based, select certificate type and assign the certificate profile you must have a separate certificate profile created for enrollment.
- VPN proxy and split tunneling: Configure split tunneling rules and any proxy settings if applicable.
- XML or custom settings: If you need advanced configuration, you can inject additional XML under the VPN policy.
- Assignments: Pick the groups that will receive this VPN profile e.g., All Windows devices or a specific group.
- Review + create: Save the profile and push it to the selected groups.
Tips:
- If you’re using certificate-based auth: create a separate certificate profile Trusted Root CA, SCEP/PKCS certificate and link it to this VPN profile.
- Always-on VPN: On Windows, you can enable Always On VPN by configuring the profile with the appropriate settings and ensuring the device is domain-joined or Hybrid AD joined.
Section 4: Create a VPN profile for iOS/iPadOS and macOS devices IKEv2 with certificate or EAP iOS/macOS steps:
- In Endpoint Manager, go to Devices > Configuration profiles.
- Create profile -> Platform: iOS/iPadOS or macOS; Profile type: VPN.
- Basic info: Name like “VPN - IKEv2 – iPhone” and description.
- Connection name: Use a recognizable name e.g., “CorpVPN”.
- Server: Enter the VPN server address.
- VPN type: Choose IKEv2.
- Authentication:
- Certificate-based: Upload/select a certificate profile ensure the device has the certificate installed via enrollment.
- EAP: Use username/password or SSO if your server supports it; configure the necessary identity and password fields.
- Shared secret: If your server uses a pre-shared key, enter it here note: IKEv2 with EAP is preferred in many cases.
- Custom settings: Use configuration profiles to push additional settings if needed DNS, split tunneling.
- Assignments: Add the user/device groups that should receive the VPN profile.
- Review + create: Save and deploy.
Tips:
- For iOS/macOS, consider using a certificate-based approach with SCEP or PKCS certs for seamless enrollment.
- Test on a small pilot group before broad deployment to catch issues with certificates or server configuration.
Section 5: Certificates and PKI considerations Cant uninstall nordvpn heres exactly how to get rid of it for good
- If you’re using certificate-based VPN, you’ll need:
- A trusted root CA installed on devices or a chain of trust with your PKI.
- Server and client certificates: client certs issued to devices; server certs on the VPN gateway.
- A certificate profile in Intune to distribute user or device certificates.
- Common issues:
- Certificate pinning mismatch or expired certs.
- Invalid certificate templates or missing EKU server authentication.
- Distribution failures due to enrollment limits or AD integration delays.
- Quick fix checklist:
- Confirm certificate templates and issuance are active.
- Validate the certificate chain on a test device.
- Re-deploy the certificate profile if needed.
Section 6: Assignments and scope
- Target groups:
- Windows devices: All Windows 10/11 devices or filtered groups.
- Apple devices: All iOS/macOS devices or specific device groups.
- Assignment types:
- Required: Force installation for compliance.
- Available: Let users enroll and install when convenient.
- Deadline and maintenance:
- Set milestones for pilot groups, collect feedback, then roll out organization-wide.
- Co-management and conditional access:
- Tie VPN usage to conditional access policies to ensure devices meet compliance before connecting to sensitive resources.
- Consider requiring device enrollment completion before VPN access is granted.
Section 7: Testing the VPN profile
- Prepare a test device in each platform family Windows, iOS, macOS.
- Steps to test:
- Enroll the device or simulate enrollment.
- Force policy refresh via Intune Company Portal app or device settings.
- Verify that the VPN profile shows up in Network settings.
- Connect to the VPN and run a quick test: ping internal resources, verify split tunneling behavior, test access to on-prem resources.
- Check event logs for VPN connection status and error codes.
- Metrics to track:
- Time from policy push to VPN connection readiness.
- Success rate of first connection after enrollment.
- User-reported issues during first use.
Section 8: Troubleshooting common VPN deployment issues
- Issue: VPN profile not appearing on device after enrollment
- Check profile assignments, scope tags, and device group membership.
- Verify user/device has enrolled successfully and signed in to the Intune portal.
- Issue: VPN connection fails or drops
- Validate server address, pre-shared key if used, and certificate validity.
- Check VPN gateway logs for authentication or tunnel establishment errors.
- Issue: Certificate-related errors
- Ensure the certificate chain is trusted on the device.
- Verify certificate templates and expiry dates.
- Issue: Conditional access blocks VPN
- Review CA policies and ensure the device is compliant e.g., encryption, threat protection.
- Issue: Always-on VPN not maintaining connection
- Confirm profile settings for auto-reconnect and tunnel persistence.
- Check device power settings and VPN re-connection policies.
Section 9: Security considerations and best practices
- Use certificate-based authentication where possible for stronger security and easier management.
- Prefer always-on VPN for seamless user experience, but ensure proper resource management to avoid battery drain on laptops.
- Separate split tunneling rules by resource type internal apps vs. internet-bound traffic to minimize leakage.
- Regularly rotate certificate and reissue profiles before expiry to prevent outages.
- Enforce strong CA policies and maintain a trusted root certificate chain in all devices.
Section 10: Real-world tips and trick shots Forticlient vpn 다운로드 설치부터 설정까지 완벽 가이드 2026년 최신: VPN 사용법, 보안 팁 및 최신 업데이트
- Use naming conventions that make it obvious which VPN and platform you’re configuring.
- Create a dedicated “VPN Pilot Group” for early feedback and a separate “VPN Rollout Group” for general deployment.
- Document error codes with quick-fix playbooks to reduce help desk time.
- Keep a running changelog for VPN profile updates and certificate renewals.
- Leverage Intune reporting to monitor deployment status by platform and group.
Section 11: Integrations and hybrid scenarios
- Integrate with Azure AD conditional access: require compliant devices and MFA for VPN access.
- Use Microsoft Defender for Endpoint to assess device health before VPN connection.
- If you’re in a hybrid environment, ensure On-Prem Active Directory and Azure AD identity sources play nicely with your VPN gateway.
- Consider third-party VPN gateways or clients if your environment requires specific features, but ensure compatibility with Intune deployment workflows.
Section 12: Deployment checklists quick reference
- Before you start:
- Define VPN type, server, and auth method.
- Prepare certificate templates and PKI distribution.
- Create device groups in Azure AD/Intune.
- During setup:
- Create Windows VPN profile with proper auth.
- Create iOS/macOS VPN profile with matching settings.
- Create and assign certificate profiles for devices/users.
- After deployment:
- Pilot test with a small group.
- Collect feedback and fix issues.
- Roll out organization-wide with staged groups.
- Ongoing:
- Monitor policy deployment status.
- Check VPN gateway logs regularly.
- Review and rotate certificates before expiry.
Frequently Asked Questions
What is Microsoft Intune, and why use it for VPN profiles?
Intune is a cloud-based service in Microsoft 365 that helps you manage devices and apps. Using Intune for VPN profiles gives you centralized control, conditional access integration, and a smoother user experience across Windows, iOS, and macOS devices.
Which VPN protocols does Intune support for profile deployment?
Intune supports common enterprise VPN protocols like IKEv2 with certificate-based or user authentication, as well as platform-specific VPN types for Windows, iOS, and macOS. You can also configure settings to enforce split tunneling and DNS behavior. The Best Free VPN for China in 2026 My Honest Take What Actually Works
Do I need a PKI for certificate-based VPN authentication?
If you want certificate-based authentication, yes. You’ll need a certificate authority to issue client certificates and a server cert on the VPN gateway. Intune can distribute user or device certificates via a certificate profile.
How do I test a VPN profile before full deployment?
Set up a small pilot group, push the VPN profile to their devices, enroll one or two test devices, and verify that the VPN connects, passes traffic, and respects split tunneling rules.
Can I enforce VPN usage with conditional access?
Yes. Tie VPN sessions to conditional access policies so only compliant devices and authenticated users can access sensitive resources when connected through VPN.
How do I handle certificate renewals in Intune?
Create a certificate profile with a renewal process and set up automatic enrollment if possible. Monitor expiry dates in Intune and alert admins ahead of expiry.
What if a user’s device is offline when the VPN profile is deployed?
Intune will apply the profile when the device comes online and checks in. Ensure users know to reconnect once their device is online. Vpn gratuita microsoft edge as melhores extensoes seguras e como instalar
Can I deploy VPN profiles for both Windows and Apple devices at the same time?
Yes. Create separate VPN profiles for each platform, with consistent naming and similar security settings to ensure a uniform experience across devices.
How do I verify that VPN traffic is correctly tunneled and secured?
Test connectivity to internal resources, verify the IP routing split vs full tunnel, and inspect VPN logs on the gateway and client devices for connection details and encryption status.
What are common mistakes when deploying VPN with Intune?
Common mistakes include misconfigured server addresses, mismatched authentication methods, expired certificates, incorrect group assignments, and not testing on pilots before full rollout.
Appendix: Quick reference templates
- Example Windows VPN profile name: “VPN - IKEv2 – Windows 11 – Always On”
- Example iOS VPN profile name: “VPN - IKEv2 – iPhone – Certificates”
- Example macOS VPN profile name: “VPN - IKEv2 – MacBook – Cert-based”
Acknowledgments This guide synthesizes best practices from enterprise IT teams deploying Intune-based VPNs in 2026, with practical steps you can apply today. If you’re exploring VPN options, consider pairing this with a reputable VPN service for off-network privacy when needed, but keep corporate traffic secured through your Intune-managed profiles. Thunder vpn setup for pc step by step guide and what you really need to know
End of post
Sources:
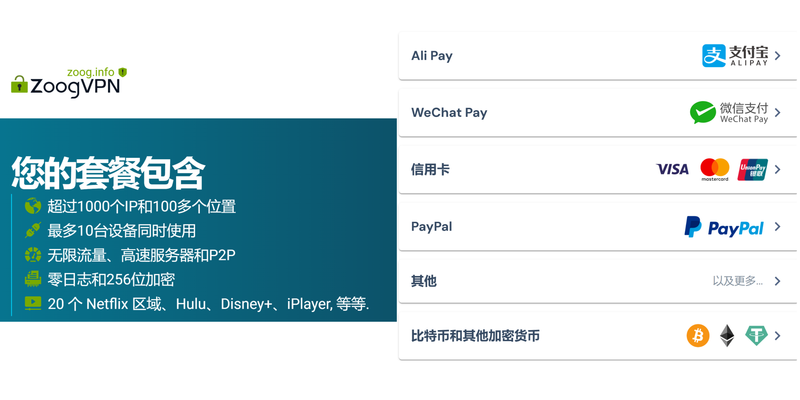
连接外网:全方位 VPN 入门到实战指南,提升上网自由与隐私
好色tv官网:VPN 使用全攻略与最佳实践
Ghost vpn google chrome
2026年翻墙好用的DNS推薦與設定指南|VPNs 深度解析 Лучшие vpn для microsoft edge в 2026 году полное руководство с purevpn и сравнение лучших вариантов
The Ultimate Guide Best VPN For Your Ugreen NAS In 2026: Faster Speeds, Stronger Privacy, Easy Setup