Use a vpn on your work computer the dos donts and why it matters
Use a vpn on your work computer the dos donts and why it matters — this guide breaks down practical steps, risks, and best practices for using a VPN at work. Quick fact: using a VPN can protect your data on public Wi‑Fi and help you access legitimate remote resources, but it can also violate company policies or slow things down if misused. Below is a practical, reader-friendly rundown with real-life tips, checklists, and scenarios to keep you safe and compliant.
Useful resources you might want to check text only: Apple Website - apple.com, Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence, VPN Security Best Practices - en.wikipedia.org/wiki/Virtual_private_network, National Cyber Security Centre - ncsc.gov.uk, Cisco Private Networking Guide - cisco.com, Privacy in the Workplace - privacyrights.org
- Quick fact: A VPN is a tool that encrypts your traffic and can mask your IP, but it won’t fix a poor password or insecure laptop.
- What you’ll get in this guide:
- Clear dos and don’ts for using a VPN on a work computer
- Reasons why VPNs matter for privacy, security, and productivity
- Real-world scenarios and decision-making tips
- A practical checklist you can edit for your workplace
- Formats you’ll find here:
- Quick-start checklist
- Step-by-step setup guide
- Pros and cons table
- Common pitfalls and how to avoid them
- Important note: Always align with your employer’s acceptable use policy. If you’re unsure, ask IT before activating any VPN on a work device.
- Affiliate note: If you’re considering a consumer-grade VPN for personal devices, you might see recommendations like NordVPN. For a quick option that labs and teams often approve, you can explore programs via the affiliate link here: NordVPN - https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
Table of contents Unlock secure internet anywhere your complete guide to fastvpn tethering
- Why use a VPN on a work computer?
- Dos: Safe, compliant VPN usage
- Don’ts: Common mistakes that can get you in trouble
- VPN use cases at work
- Security and policy alignment
- Performance and troubleshooting
- Privacy considerations
- How to choose the right VPN for work
- Real-world scenarios
- Quick-start checklist
- FAQ: frequently asked questions
Why use a VPN on a work computer?
- Protection on untrusted networks: When you’re on a coffee shop or hotel Wi‑Fi, a VPN encrypts traffic, reducing the risk of eavesdropping.
- Access to remote resources: Some teams host internal tools only on the company network or via VPN, especially for remote employees or contractors.
- Data loss prevention: A VPN can help ensure sensitive data stays on secure channels, reducing accidental data exfiltration on public networks.
- Compliance and logging: In regulated industries, VPNs can provide traceable, auditable connections that meet policy requirements.
- Risk awareness: A VPN is not a magic shield. It’s a tool that should be part of a layered security approach strong passwords, MFA, endpoint protection.
Dos: safe, compliant VPN usage
- Do read and follow your company's policy: VPN use should be documented in acceptable-use policies and security guidelines.
- Do use a company-approved VPN: Prefer IT‑provided clients with standard configurations and automatic updates.
- Do enable MFA on VPN access: Multi-factor authentication adds a critical layer of protection.
- Do keep devices updated: Regular OS and application patches strengthen your endpoint defense.
- Do monitor for strange behavior: If you notice slowdowns, errors, or credential prompts, report to IT.
- Do segregate personal and work traffic: Use containerized work sessions or separate profiles if allowed, to minimize cross-over risks.
- Do log off when not in use: End sessions when you’re done with work-critical tasks, especially on shared devices.
- Do back up important work: Ensure work files live in official repositories or cloud services with proper access controls.
Don’ts: common mistakes to avoid
- Don’t bypass IT or use unapproved VPNs: Unapproved clients can bypass security controls, leaving data exposed.
- Don’t ignore company policies on data handling: If your work involves sensitive data, follow classification and encryption guidelines.
- Don’t use personal devices without blessing: Personal devices may lack enterprise protections; only connect them if the policy allows.
- Don’t disable protection systems: Turning off antivirus or firewall for VPN purposes undermines security.
- Don’t rely on a single VPN provider for all traffic: If your company requires split-tunneling or full tunneling, follow the prescribed approach.
- Don’t log into personal accounts on work VPN: Personal email, banking, or social media on a work VPN can create data leaks.
- Don’t assume VPN = complete security: A VPN protects transport, not endpoints. If a device is compromised, a VPN won’t fix it.
- Don’t ignore performance issues: VPNs can slow down connections; notify IT rather than just blaming the network.
VPN use cases at work
- Remote access to internal apps: Intranets, HR systems, internal docs, or ticketing systems often require VPN access.
- Secure collaboration: Access to shared drives, project management tools, or code repositories while traveling.
- Compliance-driven environments: Finance, healthcare, or government-related tasks often mandate encrypted channels.
- Testing and development: Securely testing apps in internal environments from external locations.
- Incident response and forensics: When investigators need secure, auditable access to systems.
Security and policy alignment How to Set Up an OpenVPN Server on Your Ubiquiti EdgeRouter for Secure Remote Access
- Policy intersection: VPNs live at the intersection of privacy, security, and productivity. Your approach should align with corporate policies and local laws.
- Encryption standards: Modern VPNs use strong encryption AES-256 and secure protocols OpenVPN, WireGuard, IKEv2. If you’re unsure, rely on IT’s standard configuration.
- Logging and privacy: Some VPNs log connection metadata; your employer may have different retention policies. Understand what’s collected and why.
- Data handling: Even with a VPN, avoid storing sensitive data on personal devices or unsanctioned cloud storage.
Performance considerations
- Impact on speed: VPN overhead and server distance affect latency and throughput. Choose a server close to your location when possible and approved by IT.
- Split-tunneling vs. full-tunneling: Split-tunneling sends only work traffic through the VPN; full-tunneling sends all traffic. Each has security and performance trade-offs.
- Bandwidth limits: Some workplaces impose bandwidth caps or throttle heavy traffic. Plan tasks accordingly or discuss needs with IT.
Privacy considerations
- User privacy vs. employer oversight: Your employer may monitor VPN activity to ensure policy compliance. Understand what is monitored and why.
- Personal vs. work traffic: Keep personal activities off work VPN if allowed. Use separate devices or profiles whenever possible.
- Data residency: Some VPNs route traffic through external regions. Be mindful of data sovereignty rules and any location-based access restrictions.
How to choose the right VPN for work
- Seek IT-approved options: Your organization likely already has a recommended or mandated VPN client.
- Consider protocol and encryption: Look for WireGuard, OpenVPN, or IKEv2 with AES-256 encryption.
- Client compatibility: Ensure the VPN works on your operating system Windows, macOS, Linux and supports your hardware.
- Reliability and support: Prioritize vendors with strong uptime, clear incident response, and good IT support.
- Policy-friendly features: Split-tunneling, kill switch, and automatic reconnect can be important, but ensure they align with policy.
- Auditing and compliance: For regulated roles, choose VPNs with robust logging controls and compliance certifications.
Real-world scenarios
Scenario A: Remote worker on a public Wi‑Fi network How to use a vpn with microsoft edge on iphone and ipad for enhanced privacy
- Action: Connect via approved VPN, ensure MFA is enabled, avoid accessing sensitive personal accounts on the same device.
- Outcome: Encrypted traffic, reduced risk of eavesdropping, maintained access to internal tools.
Scenario B: Accessing sensitive HR data on a personal laptop
- Action: Use a company-provided device or ensure the personal device is managed by IT, with approved security controls.
- Outcome: Data remains secure, risk of data leakage is minimized.
Scenario C: Team software deployment in a distributed environment
- Action: Use VPN with split-tunneling configured as per policy, access only necessary internal resources.
- Outcome: Efficient workflows without unnecessary exposure or performance hits.
Scenario D: Incident response during a security event
- Action: IT directs the VPN configuration for forensics and evidence collection, ensure chain of custody.
- Outcome: Clear, auditable access while preserving data integrity.
Scenario E: Compliance audit week
- Action: Review VPN logs, verify MFA usage, confirm encryption standards, and document policy adherence.
- Outcome: Smooth audit with demonstrable security controls.
Practical deep-dive: setup steps you can follow Soundcloud not working with vpn heres how to fix it fast
- Step 1: Confirm policy and obtain permission
- Check the employee handbook, IT portal, or contact your security team.
- Step 2: Install the approved VPN client
- Use the official IT-provided installer to avoid misconfigurations.
- Step 3: Configure the connection
- Enter server address, enable MFA, choose the recommended protocol often WireGuard or OpenVPN.
- Step 4: Test connectivity
- Connect to a non-sensitive internal resource first to verify access.
- Step 5: Enable security features
- Turn on kill switch, DNS leak protection, and auto-reconnect if available.
- Step 6: Verify split-tunneling settings
- Confirm which traffic goes through VPN versus direct internet access, per policy.
- Step 7: Monitor performance
- Watch for latency spikes and report to IT if you notice unusual behavior.
- Step 8: Maintain hygiene
- Keep your device updated, use strong passwords, and enable MFA.
FAQ: frequently asked questions
How does a VPN protect my work data on a coffee shop network?
A VPN encrypts your traffic so others on the same network can’t read it. This helps protect sensitive information, like login credentials and internal documents, from eavesdroppers.
Can I use a personal VPN for work tasks?
Usually not. Most employers require using a company-approved VPN client to ensure security controls and policy compliance. Always check with IT before using a personal VPN.
What’s the difference between split-tunneling and full tunneling?
Split-tunneling routes only work-related traffic through the VPN, while full tunneling sends all traffic through the VPN. Split-tunneling can improve performance but may introduce privacy or security considerations depending on policy.
What is a VPN kill switch?
A kill switch automatically cuts internet traffic if the VPN disconnects, preventing data from leaking outside the encrypted tunnel. Expressvpn not working with google heres how to fix it fast: Quick Fixes, Tips, and VPN Best Practices
Is a VPN enough to protect against malware on a work device?
No. A VPN protects traffic in transit but not the device itself. Use endpoint protection, regular software updates, and safe browsing practices.
Do VPNs log my activity?
Some VPNs log connection metadata or usage. Company policies typically govern what is logged. If privacy is a concern, review policy details with IT.
Can a VPN cause slower internet speeds?
Yes. Encryption overhead and routing through VPN servers can add latency. Use the closest approved server and a higher-performance plan if allowed.
Why do employers require MFA with VPN access?
MFA adds a second layer of verification, making it harder for attackers to gain access even if a password is compromised.
What happens if the VPN connection drops?
If the VPN has a kill switch, all traffic will be blocked until the VPN reconnects. If not, traffic may leak temporarily, which is why kill switches are recommended. Comment activer le reseau securise vpn gratuit de microsoft edge et autres options VPN adaptées au Canada
How should I handle sensitive data while using a VPN?
Follow data handling policies, store files in approved repositories, and avoid saving sensitive material on personal devices unless explicitly allowed.
Checklist: quick-start for your work VPN
- Confirm you’re using an approved VPN client
- Enable MFA for VPN access
- Keep your device updated with the latest security patches
- Use a strong, unique password and password manager
- Enable the VPN kill switch and DNS leak protection
- Verify split-tunneling settings match policy
- Log off when not using work resources
- Avoid mixing personal activities with work traffic on the VPN
- Report any issues to IT promptly
Why this matters for you
- You’re protecting sensitive company data from modern threats, especially on public networks.
- You’re ensuring you stay compliant with internal policies and regulatory requirements.
- You’re helping IT teams maintain visibility and control over corporate resources, which makes your work smoother and safer for everyone.
Final thoughts Using a VPN on a work computer is a smart move when done right. It’s a tool that, when paired with good security hygiene and policy adherence, lets you work securely from anywhere. If you’re unsure about the exact steps or which client to deploy, reach out to your IT department. And if you’re evaluating a consumer VPN for personal use, consider the affiliate option above as a starting point for a resource that’s easy to access and widely supported.
Frequently Asked Questions Npm Not Working With VPN Here’s How To Fix It
How can I tell if my VPN is correctly configured?
Check your connection status in the VPN client, verify you can access internal resources, and perform a DNS leak test your DNS should resolve to internal or enterprise DNS, not your ISP’s. If in doubt, contact IT.
Can I use a VPN to bypass geo-restrictions at work?
No. Bypassing geo-restrictions or policy controls is typically against policy and could have consequences. Always follow the rules.
What’s the best practice for handling official documents when connected via VPN?
Store official documents in approved company repositories or cloud storage with proper access controls. Do not download or store sensitive data on personal devices.
Is it safer to use a VPN on a corporate device or a personal device?
A corporate device with an approved VPN is generally safer because it’s managed by IT, has security controls, and follows policy. Personal devices can be compliant if IT provides the necessary protections and approvals.
Should I use a VPN when working from home?
Yes, especially if you access internal systems or handle sensitive data. Home networks can be less secure than corporate networks, so a VPN adds a protective layer. Best free vpns for roblox pc in 2026 play safely without breaking the bank
How often should VPN software be updated?
Keep the VPN client and device OS up to date. IT usually pushes updates, and you should install them promptly to maintain security.
Can a VPN protect me from phishing?
A VPN mainly protects data in transit. It does not prevent phishing attempts. Use email hygiene, MFA, and security awareness training to guard against phishing.
What are some signs that my VPN is not functioning properly?
Frequent disconnects, alarms in the VPN client, or inability to access internal resources can indicate a misconfiguration or outage. Contact IT for support.
What should I do if I suspect a VPN security incident?
Immediately isolate affected resources, report to IT, preserve logs if possible, and follow the incident response plan. Do not attempt to fix it yourself if you’re not trained.
Sources:
How to enable line number in sql server step by step guide How to Disable NordVPN’s Password Manager NordPass Quickly and Safely
Nordvpn not working with amazon prime heres how to fix it: Quick Fixes, Tips, and Alternatives
Is 1password a vpn what you need to know for better online security
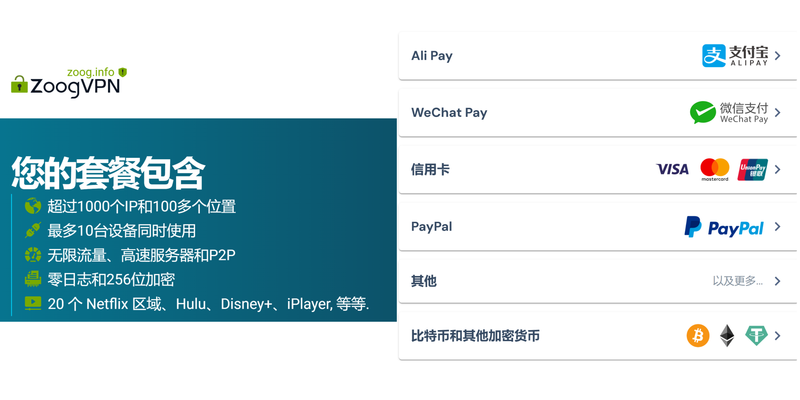
Nordic vpn 多重护航:全面评测与实用指南,结合 SEO 优化与实用建议
Como obtener nordvpn anual al mejor precio guia completa 2026