Setting up intune per app vpn with globalprotect for secure remote access and related best practices
Setting up intune per app vpn with globalprotect for secure remote access is all about giving users a seamless, secure connection to corporate resources without forcing full-device VPN. Quick facts: you can integrate Microsoft Intune app protection policies with per-app VPN to ensure only the intended apps tunnel traffic, while GlobalProtect handles secure remote access with consistent, policy-driven controls. This guide walks you through the setup, offers practical tips, and shares best practices backed by up-to-date data.
What you’ll learn
- Why per-app VPN matters for security and user experience
- The components involved: Intune, GlobalProtect, and your network gateway
- Step-by-step setup: configure per-app VPN, publish GlobalProtect, assign profiles, and verify
- Common pitfalls and troubleshooting steps
- Advanced tips: conditional access, device compliance, and reporting
- Useful resources and reference links at the end
Quick facts and benefits Outsmarting the unsafe proxy or vpn detected on now gg your complete guide
- Per-app VPN minimizes risk by only tunneling traffic from approved apps
- Centralized control through Intune simplifies policy management
- GlobalProtect provides a consistent remote access experience across devices
- You can combine conditional access with app-based VPN for stronger security
What is per-app VPN and why it matters Per-app VPN is a feature that routes only select apps’ traffic through a VPN tunnel, leaving other apps to use direct internet access. This approach reduces overhead on the device and improves performance while still protecting sensitive data. For organizations using Microsoft Intune, you can push per-app VPN profiles to users’ devices, tying them to specific enterprise apps. GlobalProtect acts as the secure gateway that handles the VPN connection, user authentication, and policy enforcement.
Key components and prerequisites
- Microsoft Intune: for device and app management, policies, and per-app VPN configuration
- GlobalProtect by Palo Alto Networks: the VPN gateway and client that establishes the secure tunnel
- VPN gateway and portal URLs: your GlobalProtect gateway must be reachable from managed devices
- Azure Active Directory AAD or on-premises Active Directory for user authentication and conditional access
- App list: identify which apps will use the VPN tunnel
- Certificates or SAML/OIDC-based authentication: depending on your setup
- Network/resource planning: ensure the resources accessed through the VPN are properly segmented and secured
Step-by-step setup overview Note: this is a high-level flow; specifics may vary by your GlobalProtect version and Intune configuration.
- Plan and document
- List apps to tunnel: e.g., internal CRM, file shares, DMS apps
- Define access rules: who can access which resources, from which locations
- Prepare GlobalProtect gateway details: portal URL, gateway hostname, and authentication methods
- Decide on certificate strategy: device certs, user certs, or other methods
- Prepare GlobalProtect gateway and portal
- Set up the GlobalProtect portal and gateways in your Palo Alto Networks firewall or Panorama
- Configure authentication: SAML/OIDC or certificate-based, aligned with Intune and Azure AD
- Create and publish a per-app VPN policy if supported or standard VPN policy with app-based segmentation
- Create and publish per-app VPN profile in Intune
- In Endpoint Manager admin center, go to Profiles > Create profile
- Platform: iOS/iPadOS or macOS or Android, depending on your environment
- Profile type: VPN
- VPN connection type: GlobalProtect
- Server address: enter the GlobalProtect gateway/portal URL
- Authentication: use the same method as your gateway certificate or SAML, etc.
- Assign the profile to the user/device groups that need access
- Configure per-app VPN for specific apps
- In Intune, use App configuration policies or per-app VPN assignments to tie the VPN profile to specific apps
- Define the apps that should trigger the VPN tunnel for iOS, you configure per-app VPN via Endpoint Management and select the app bundle IDs
- Ensure proper bundle IDs and entitlements are used to prevent conflicts
- Deploy and verify the client
- Have users install the GlobalProtect client and any required dependencies via Intune-required apps
- Ensure the Intune VPN profile installs automatically
- Verify per-app VPN is functional by launching a connected app and checking if its traffic uses the VPN tunnel
- Enforce conditional access and device compliance
- Use Azure AD conditional access to require device compliance for VPN access
- Combine policies like device health, location-based access, and user risk signals to tighten security
- Consider requiring device enrollment and MDM enrollment for all remote workers
- Monitoring and reporting
- Monitor VPN connection status, user sign-ins, and app-level VPN usage in Intune and GlobalProtect dashboards
- Set up alerts for failed authentications, unusual traffic patterns, or non-compliant devices
- Regularly review access logs and adjust policies as needed
Best practices for a smooth rollout
- Start with a pilot: choose a small user group to validate configurations before broad rollout
- Favor per-app VPN for high-value apps first, then expand to more apps
- Keep user communication simple: provide a short guide on how to connect and what to expect
- Maintain clear naming conventions for VPN profiles and app mappings
- Regularly update both Intune and GlobalProtect clients to stay current with security fixes
- Align VPN access with your data classification policies to minimize exposure
Troubleshooting common issues Лучшие vpn для microsoft edge в 2026 году полное руководство с purevpn и сравнение лучших вариантов
- Issue: VPN fails to start after enrolling a device
- Check Intune profile assignment and device enrollment status
- Verify gateway URL, authentication method, and certificate validity
- Issue: Traffic not routing through VPN for the target app
- Confirm the app is included in the per-app VPN policy
- Validate the app’s bundle ID or package name matches exactly
- Issue: Slow VPN performance
- Check gateway capacity, load balancing, and network latency
- Review split-tunneling settings if applicable
- Issue: Certificate or auth errors
- Confirm the certificate chain is trusted on devices
- Ensure SAML/OIDC app registration in Azure AD is correctly configured
- Issue: Access denied by conditional access
- Verify device compliance policies and user location constraints
- Review conditional access policy conditions and grant controls
Security considerations and compliance
- Principle of least privilege: users get VPN access only to what they need
- Regularly rotate credentials and certificates and enforce strong authentication
- Enable device posture checks OS version, jailbreak/root status, disk encryption
- Use threat prevention features in GlobalProtect timers and firewall policies
- Audit and log all VPN sessions and access attempts for compliance reporting
Advanced configurations and tips
- Multi-geo deployments: if your users are global, ensure GlobalProtect gateways cover multiple regions
- Certificate-based authentication: use client certificates for stronger trust
- Separate tunnels by app type: for highly sensitive apps, route all their traffic through VPN
- Use alternative identity providers: if you’re not fully on Azure AD, integrate with your on-prem AD via ADFS or similar
- Consider split-tunneling carefully: it can improve performance but may increase risk if not managed properly
- Employ network access controls in the gateway to limit resource access by IP, subnet, or user group
Integration with other security layers
- Conditional Access + per-app VPN creates a strong security posture
- Combine with Data Loss Prevention DLP and endpoint detection and response EDR
- Use identity protection and risk-based authentication for outside users
Comparing OS support and limitations
- iOS/iPadOS: per-app VPN is well-supported; ensure the app supports VPN extension
- macOS: per-app VPN is possible with Intune and GlobalProtect, check app entitlements
- Android: per-app VPN capabilities exist but may differ by OEM and device model
- Windows: per-app VPN approaches exist but often rely on full-device VPN or app traffic rules; verify with your GlobalProtect setup
Performance tips and optimization Thunder vpn setup for pc step by step guide and what you really need to know
- Use regional gateways to reduce latency
- Enable caching and intelligent routing where supported
- Monitor VPN session duration and re-authentication intervals to balance user experience and security
Helpful resources and references
- Microsoft Intune documentation for per-app VPN configuration
- Palo Alto Networks GlobalProtect deployment guides
- Azure Active Directory conditional access policy references
- IT security best practices for remote access and VPNs
Frequently asked questions
What is per-app VPN and how does it differ from regular VPN?
Per-app VPN tunnels traffic only from selected apps, while regular VPN routes all traffic from the device. This reduces overhead and improves performance and security by limiting exposure.
Can I use per-app VPN with GlobalProtect and Intune at the same time?
Yes, you can configure per-app VPN in Intune and use GlobalProtect as the gateway to enforce secure tunnels for designated apps.
What platforms are supported for per-app VPN with Intune?
IOS, iPadOS, macOS, and Android are commonly supported, with some variations in features across platforms and device configurations. Vpn gratuita microsoft edge as melhores extensoes seguras e como instalar
How do I assign VPN profiles to specific users or devices?
Through Intune device groups or user groups. Create a profile, configure GlobalProtect settings, and assign to the appropriate group.
How do I verify that a VPN connection is active for a given app?
Launch the app and check the VPN status in the device’s network settings or GlobalProtect client, and monitor the app’s network traffic to confirm it’s tunneled.
What authentication methods work best with GlobalProtect and Intune?
Certificate-based authentication or SAML/OIDC-based single sign-on are common and secure options. Choose the method that aligns with your identity provider.
How do I enforce device compliance for VPN access?
Use Azure AD conditional access policies that require device enrollment and compliance with your security baselines before allowing VPN access.
Can I restrict VPN access by location?
Yes, with conditional access and gateway policies you can restrict access to specific locations or networks. How to create a vpn profile in microsoft intune step by step guide 2026
How do I monitor VPN usage and incidents?
Use Intune reporting, GlobalProtect analytics, and your firewall logs to track connection status, user activity, and security events.
What are common pitfalls to avoid?
- Using a broad VPN scope that tunnels all traffic unnecessarily
- Misconfiguring app bundle IDs or gateway URLs
- Skipping conditional access or device compliance checks
- Failing to keep clients and gateways updated with security patches
Useful URLs and Resources
- Microsoft Intune documentation - intune.microsoft.com
- Azure AD Conditional Access - docs.microsoft.com/en-us/azure/active-directory/conditional-access
- Palo Alto Networks GlobalProtect - paloaltonetworks.com/products/globalprotect
- Intune per-app VPN setup guides - docs.microsoft.com/en-us/mem/endpoint-manager
- App configuration policies in Intune - docs.microsoft.com/en-us/mem/configmgr/core/plan-design/devices/modern-management
- Best practices for secure remote access - en.wikipedia.org/wiki/Remote_access_security
- VPN performance optimization - cisco.com/blogs/techwire/vpn-performance
- GlobalProtect gateway and portal configuration examples - paloaltonetworks.com/resources
- Device compliance and security baseline guidance - microsoft.com/security
Affiliate note NordVPN resources and related security tools can complement your corporate setup for auxiliary protection on personal devices. For more information, check out the NordVPN resource in the article annotations.
Sources:
Radmin vpn mac 与相关VPNs:完整指南,含设置、安全性与实用比较
Where is my ip location with nordvpn your complete guide: Find, Verify, and Understand IP Location with NordVPN Proton ⭐ vpn 무료 사용법 완벽 가이드 속도 보안 설정 총정
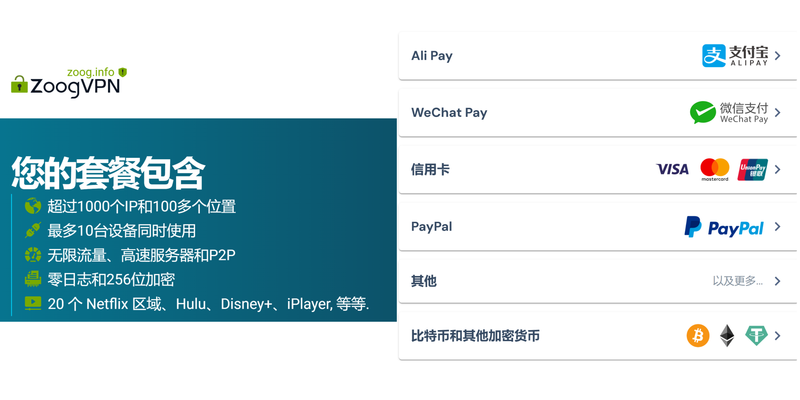
好用的机场订阅|全面指南與最新TIPs,VPN專題解密
Missav转 VPN 安全指南:提升隐私、解锁内容与高速连接的全面攻略
Ikunn vpn:全面解析、使用技巧与实用指南,涵盖隐私保护、解锁与测速